This Article will provide details about Docker security . How we can detect security vulnerabilities before it going into production . Automated way by integrating security vulnerabilities tool in pipeline and details about how we can fix security vulnerabilities by modifying Dockerfiles .
Why Docker security is more important ?
Vulnerable OS and non-OS packages and ensure that non-secure and non-compliant images are not promoted in trust production registries .
1. How to Install and Set Up Anchore CLI on Ubuntu 22.04
2. How to Install and Set Up Anchore Engine with Docker Compose
- Start Anchore Engine Services:
docker-compose up -d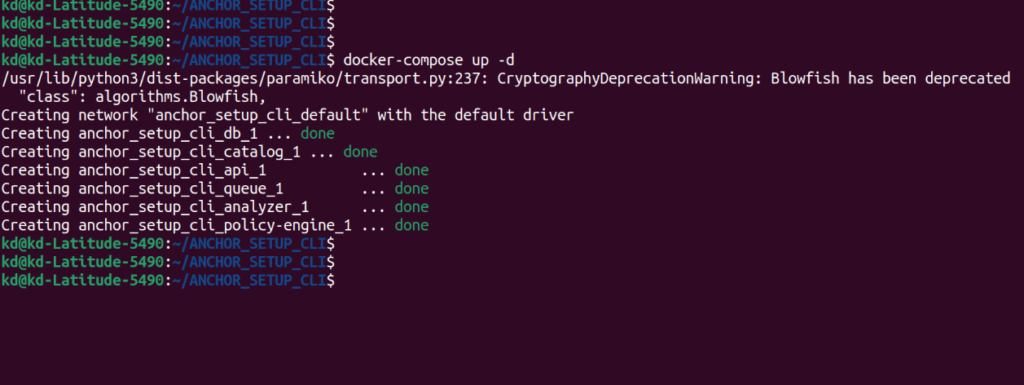
With this command, you can start all the services of Anchore Engine in the background.
- Check Services Status:
docker-compose ps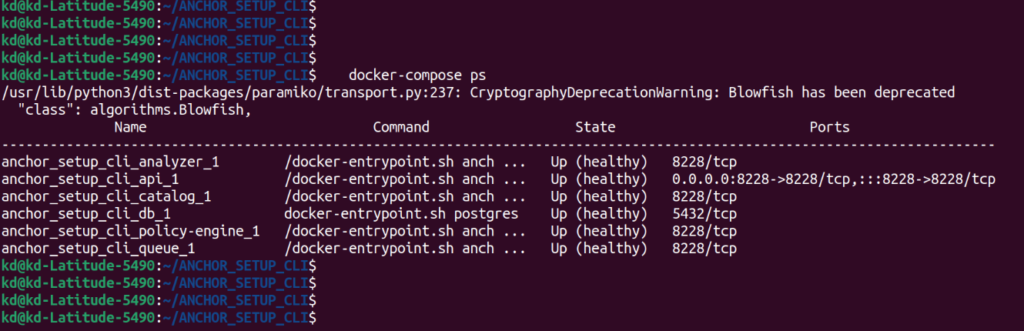
With this command, you can check the status of all services of the Anchore Engine.
- Check Anchore Engine System Status:
docker-compose exec api anchore-cli system status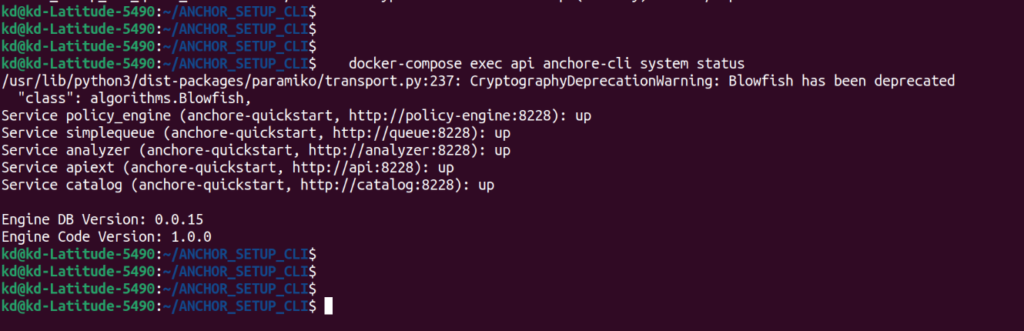
With this command, you can check the system status of the Anchore Engine.
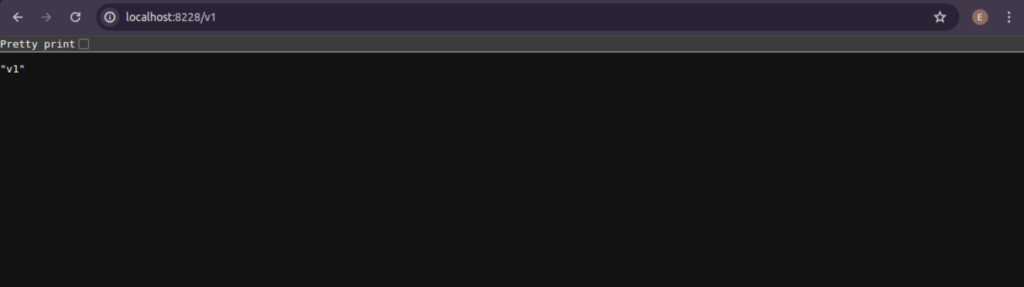
- Access Anchore Engine UI:
To access the Anchore Engine UI, you can open the URL http://localhost:8228/ in your browser.
http://localhost:8228/v1
5. Stop Anchore Engine Services:
docker-compose down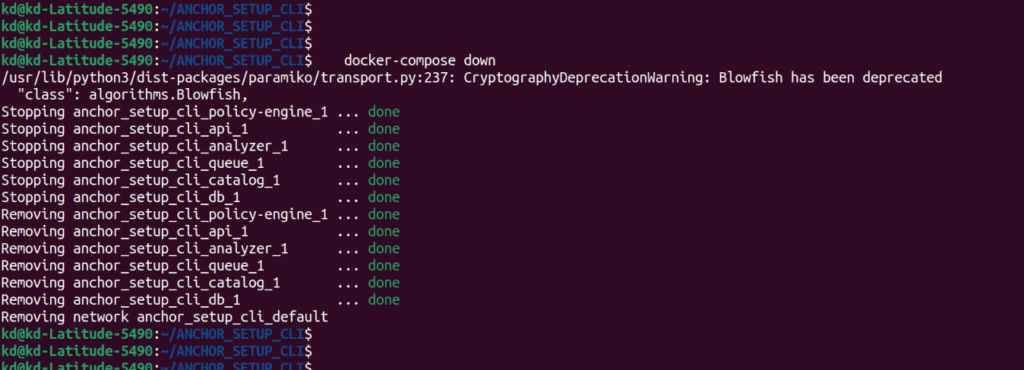
With this command, you can stop the Anchore Engine services.
# Check Anchore API endpoint using curl (replace your ip address)
curl http://192.168.170.251:8228/v1
# Check Anchore Engine status using anchore-cli with specified URL, username, and password (replace your ip address)
anchore-cli --u admin --p foobar --url http://192.168.170.251:8228/v1 system status
# Set environment variables for Anchore CLI (replace your ip address)
export ANCHORE_CLI_URL=http://192.168.170.251:8228/v1
export ANCHORE_CLI_USER=admin
export ANCHORE_CLI_PASS=foobar

How to use this anchore engine
- Add Image: Add a Docker image to Anchore Engine for analysis.
anchore-cli image add nginx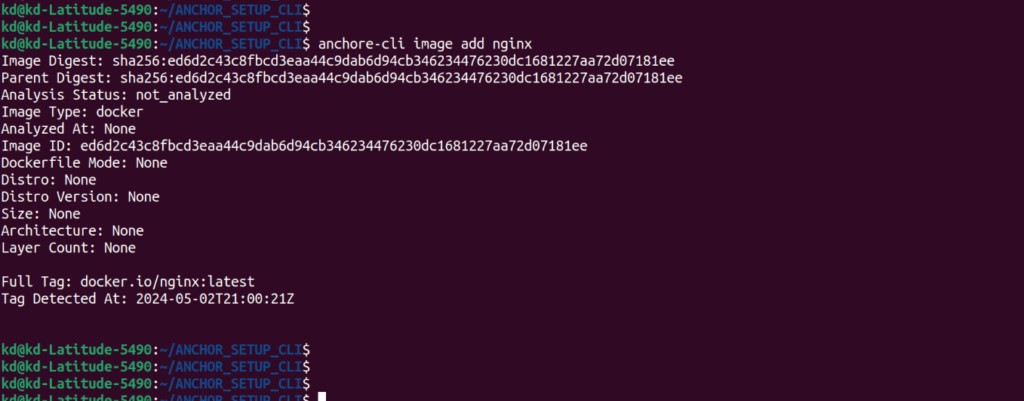
- List Images: List all Docker images currently known to Anchore Engine.
anchore-cli image list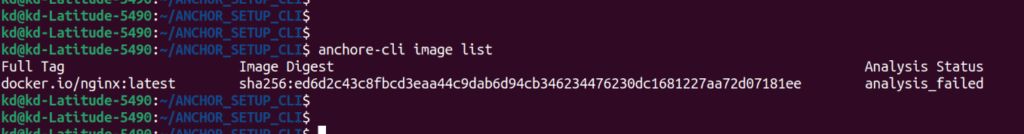
- Get Image Summary: Retrieve a summary of information about a specific Docker image.
anchore-cli image get nginx
- Get Image Vulnerabilities: Retrieve vulnerability information for a specific Docker image.
anchore-cli image vuln nginx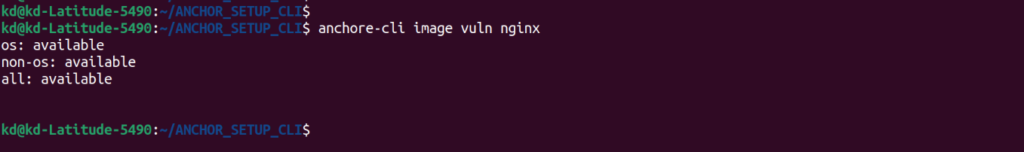
- Get Image Policy Evaluation: Retrieve policy evaluation results for a specific Docker image.
anchore-cli image get nginx 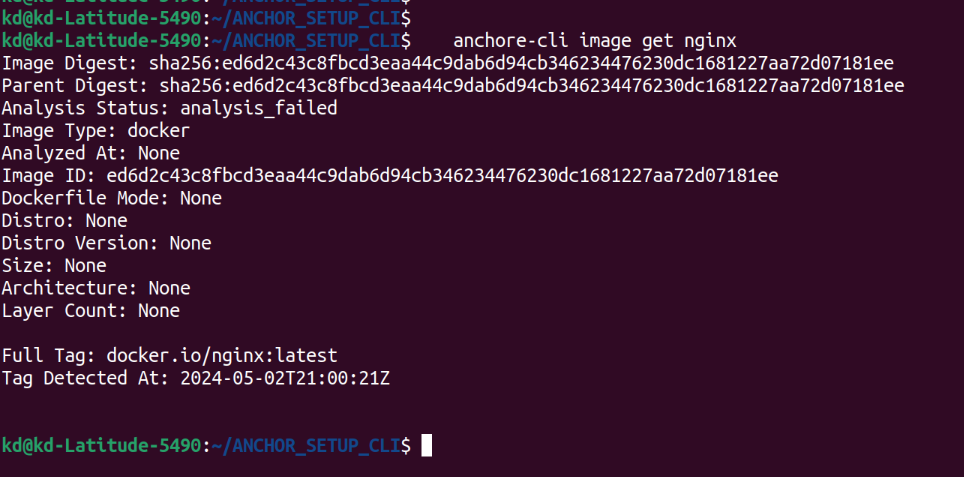
- Get Image Content: Retrieve detailed content information for a specific Docker image.
anchore-cli image content nginx
- Delete Image: Delete a specific Docker image from Anchore Engine.
anchore-cli image delete nginx- How to use Claude tool in MCP - May 23, 2026
- What is MCP (Model Context Protocol)? And Agent vs MCP - May 21, 2026
- GitHub Actions Tutorial: 7 Easy Steps for CI/CD Automation - May 18, 2026